
Primer on the Costs of Cyber Espionage
Cyber espionage is the use of cyber tools and techniques to gather intelligence or steal sensitive information from targeted entities. This form of espionage poses significant risks to national security, economic stability and corporate integrity. Given the complex and often hidden nature of cyber espionage activities, accurately measuring their costs presents a significant challenge. Traditional accounting methods and mental models of espionage may fall short in capturing the full impact of cyber espionage and recovery from these incidents, particularly those costs related to intangible assets such as brand reputation and competitive advantage. Measurement methodologies today may not be effective in capturing the full range of costs in years to come as actors adapt and tactics like supply chain attacks post costs to an ever-wider range of third parties as part of cyber espionage targeting a particular organization. Accurately measuring the costs associated with cyber espionage is thus an evolving problem space with direct implications for policy.

Strategic Authoritarian Narratives in the Sahel
In recent years, countries in the Sahel region of Africa have faced widespread insecurity and instability. Stretching across the northern tier of sub-Saharan Africa, Sahel countries Niger, Mali, and Burkina Faso have all experienced a series of military coups and rising levels of right-wing extremism. Poverty, environmental degradation, and competition for scarce resources like uranium, have further exacerbated this situation, creating a volatile mix of factors that have fueled social unrest and enabled the expansion of terrorist groups operating in these countries.

Technical infrastructure as a hidden terrain of disinformation
While social media disinformation has received significant academic and policy attention, more consequential forms of intentional manipulation target the underlying digital infrastructures upon which society depends. Infrastructure-based deception, less visible than deception targeting content and platforms, has consequences for internet security, stability and trust. This article examines terrains of disinformation in digital infrastructure, including in the Domain Name System, access and interconnection, public key infrastructures, cyber-physical systems and emerging technologies. Infrastructure disinformation is largely a cybersecurity problem. By bringing technical infrastructure into the epistemic realm of disinformation, this paper shifts policy conversations around content moderation to encompass stronger cybersecurity architectures.

Disinformation and Identity-Based Violence
Disinformation spread via digital technologies is accelerating and exacerbating violence globally. There is an urgency to understand how coordinated disinformation campaigns rely on identity-based disinformation that weaponizes racism, sexism, and xenophobia to incite violence against individuals and marginalized communities, stifle social movements, and silence the press.
The purposeful spread and amplification of identity-based disinformation is not just an individual expression of individual bias but instead represents the systematic weaponization of discrimination to make hateful narratives go viral. At the core of identity-based disinformation is the exploitation of individuals’ or groups’ senses of identity, belonging, and social standing.
Responding to identity-based disinformation will require technical and human responses that are collaborative, locally relevant, and community-driven. Given the extent of the harms posed by identity-based disinformation, there is a continued need to develop, implement, and improve responses.

State-sponsored cyber attacks and co-movements in stock market returns: evidence from US cybersecurity defense contractors
As cyber threats become increasingly central to international politics, state-sponsored cyber attacks have become an instrument of geopolitical leverage. Emerging evidence shows that states are increasingly turning to cyber industrial espionage to boost the competitiveness of domestic firms. Leveraging data on cyber attacks and stock market returns for a sample of U.S. based cybersecurity defense contractors from 2000 to 2020, this study empirically demonstrates that an escalation in the intensity of state-sponsored cyber attacks prompts a behavioral shift among investors and regulators, leading to increased co-movement in firms’ stock returns.

Exporting Autocracy: How Foreign Influence Operations Shape Democratic Attitudes
What impact do foreign authoritarian influence operations (FIOs) have on democracy? By some measures, nearly all the hard-won democratic gains from the previous 35 years had disappeared by 2022 (Varieties of Democracy 2023). Since these declines corresponded with a steep increase in disinformation, numerous scholars argue that FIOs contributed to these democratic setbacks (Diamond 2019; Dobson, Masoud, and Walker 2023). Other research has questioned the evidence of such backsliding (Little and Meng 2024; Arriola, Rakner, and Van de Walle 2023), or claimed more generally that information campaigns have only marginal political effects (Eady, Paskhalis, Zilinsky et al. 2023). Through an examination of democratic attitudes in 15 African countries between 2009 and 2023, we present preliminary but compelling evidence that autocrats export authoritarianism.

Misinformed about Misinformation: On the polarizing discourse on misinformation and its consequences for the field
For almost a decade, the study of misinformation has taken priority among policy circles, political elites, academic institutions, non-profit organizations, and the media. Substantial resources have been dedicated to identifying its effects, how and why it spreads, and how to mitigate its harm. Yet, despite these efforts, it can sometimes feel as if the field is no closer to answering basic questions about misinformation’s real-world impacts, such as its effects on elections or links to extremism and radicalization.

Mythical Beasts and Where to Find Them
Despite its contribution to human rights harms and national security risks, the proliferation of spyware remains rife. A significant channel for this proliferation is sale through a global market, of which most public information is known about only a handful of vendors. While some of these entities have achieved infamy, like NSO Group and the Intellexa Consortium, most others have largely flown under the radar.
The Mythical Beasts project addresses this meaningful gap in contemporary public analysis on spyware proliferation, pulling back the curtain on the connections between 435 entities across forty-two countries in the global spyware market. These vendors exist in a web of relationships with investors, holding companies, partners, and individuals often domiciled in different jurisdictions.
Secret Cyber Wars: Why States Are Increasingly Turning to Economic Espionage and How Cyber Proxies Play a Key Role
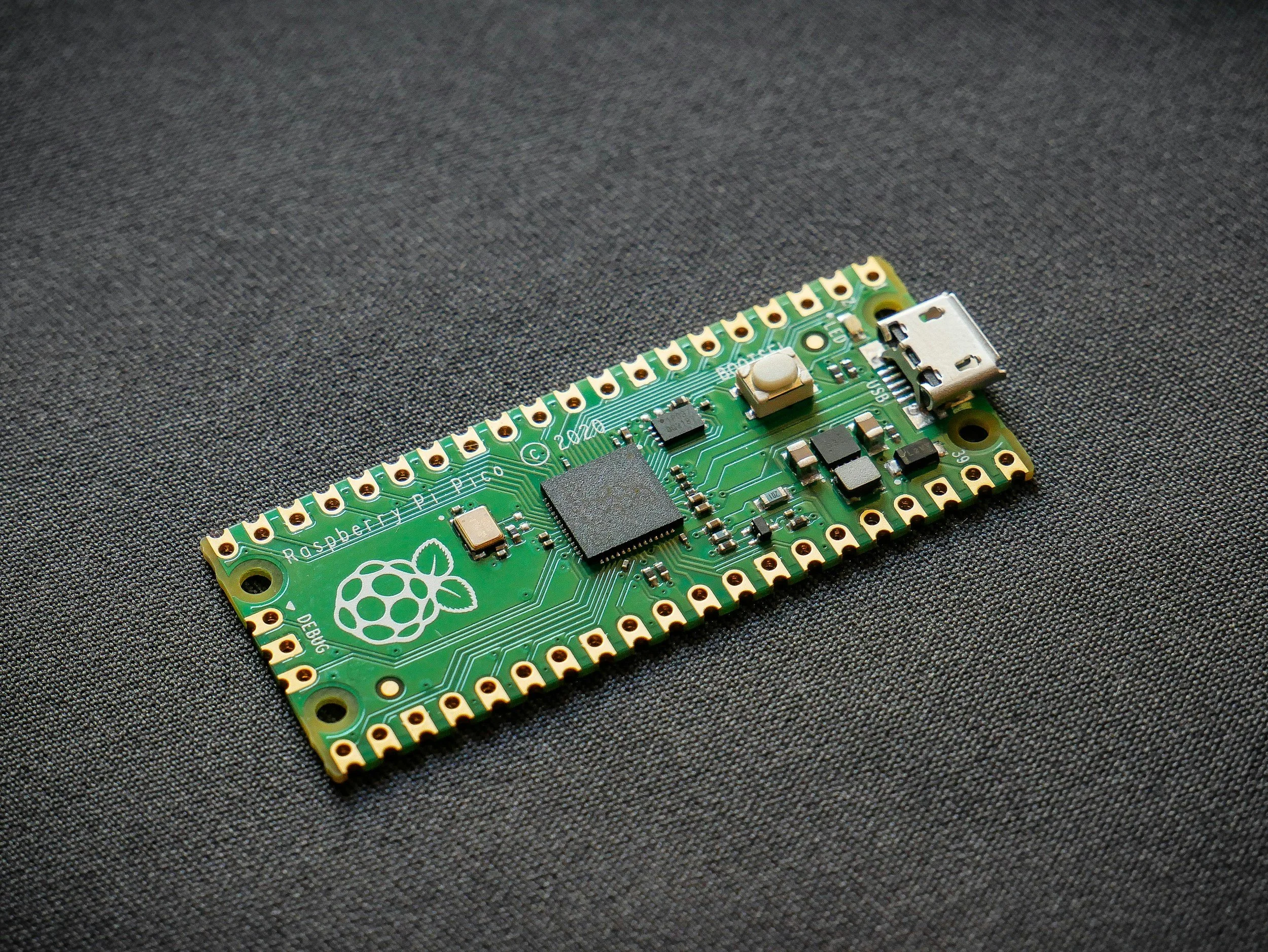
In September 2001, operatives for Procter & Gamble were caught diving in dumpsters outside a Unilever facility in Chicago in search of documents and other discarded items containing confidential information about Unilever’s hair care products business. To avoid litigation and the negative publicity that often accompanies such disputes, the companies quietly reached a negotiated settlement where Procter & Gamble agreed to not use any of the information obtained. This early example illustrates the ongoing vulnerability companies face regarding data security. In today’s corporate environment where digital data storage is the norm, companies now have to be wary of not only paper documents but also discarded storage devices like hard drives, USBs, and even old office equipment that might store digital data.

Book Review Fight for the Final Frontier: Irregular Warfare in Space
A seasoned scholar, strategist, and expert in space policy and strategy, Dr. John J. Klein is well-versed in applying strategic theory to the space domain. In his new book, Fight for the Final Frontier: Irregular Warfare in Space (2023), Klein argues that irregular warfare, in both its military and nonmilitary forms, is a vital and underutilized concept for understanding malicious activities in space and the nature of space warfare. His argument draws on a diverse list of strategic theorists, historians, and contemporary policy analyses. Klein weaves these sources together persuasively, providing an accessible overview of a technologically demanding subject. Policy generalists and students, along with veteran analysts of space policy, will benefit from his account.

Book Review - Cyber Threats & Nuclear Weapons
As the world’s infrastructure becomes increasingly interconnected, more critical systems are exposed to cyber threats. A cyber threat is a malicious act intended to steal, damage, or disrupt digital data. Cyber threats seek to turn potential security vulnerabilities into attacks on systems and networks.

Markets Matter - A Glance into the Spyware Industry
The Intellexa Consortium, a complex web of holding companies and vendors for spyware and related services, have been the subject of recent, extensive sanctions by the US Department of the Treasury and the focus of reporting by the European Investigative Collaborations among others. The Consortium represents a compelling example of spyware vendors in the context of the market in which they operate—one which helps facilitate the commercial sale of software driving both human rights and national security risk. This paper addresses an international policy effort among US partners and allies, led by the French and British governments, as well as a surge of US policy attention to address the proliferation of this spyware.

Small Satellites and International Security
Orbiting satellites perform many tasks: communications, broadcasting, weather forecasting, earth observation, intelligence-gathering, and scientific research. The first satellite, launched in 1957, was a modest metal sphere containing a simple radio transmitter. Since then, satellites have grown in size and complexity. Many are visible to anyone with a reasonably powerful backyard telescope.

Who spies on whom? Unravelling the puzzle of state-sponsored cyber economic espionage
Traditional conceptions of state-sponsored cyber economic espionage suggest that countries with different product profiles should experience high levels of espionage between them. However, this is not what we observe empirically. This article offers new insights into the strategic calculations that underpin state-sponsored cyber espionage and challenges scholars and policymakers to rethink the dynamics of international economic competition and security in the digital age.

New Technology and Nuclear Risk
In 2006, two leading scholars of the nuclear era warned that the age of mutually assured destruction (MAD) was ending. Seventeen years later, the authors are doubling down on these claims, arguing that the outbreak of new conventional conflicts has changed nuclear decision making, increasing the threat of coercive nuclear escalation. In an age of new technology, this warning is more pertinent than ever. The rapid introduction of emerging technologies and their weaponization raises concerns about maintaining strategic stability.

Cyber economic espionage: a framework for future research
The study of economic espionage has been dominated by scholarship focused on its legal and legislative aspects. However, economic espionage has important political economy dynamics that have largely gone unexplored. This is unfortunate because recent technological advances and changing dynamics of interstate economic competition mean there is much scope for a progressive research agenda focused on the political economy of cyber economic espionage. This chapter outlines key under-researched areas where the most progress is possible. I advocate for studies focused on examinations of the motives of cyber economic espionage, its conduct, how governments respond to it and how it is influenced by economic interdependence.

Hackers for Hire: Proxy Warfare in the Cyber Realm
In February 2018, the cybersecurity firm FireEye published a report detailing the activities of a hacker group called APT37, which had carried out a series of cyberattacks across Asia. The report assessed “with high confidence” that the group was acting on behalf of the North Korean government. This is just one example of a rising trend, as states increasingly turn to “cyber proxies”—hacker groups that carry out cyber operations on behalf of or in concert with nation states.
Accountability and cyber conflict: examining institutional constraints on the use of cyber proxies
As state-sponsored cyber operations have proliferated, some states are outsourcing these operations to non-state cyber proxies. However, given the relative ease of outsourcing cyber operations, it is puzzling why more states are not engaged in this practice. This study examines how domestic accountability institutions potentially explain this restraint in the use of cyber proxies.

Espionage attempts like the SolarWinds hack are inevitable, so it’s safer to focus on defense – not retaliation
In the wake of the major espionage operation in which people alleged to be Russian government agents infiltrated the digital networks of the U.S. Defense, Treasury and Homeland Security departments – as well as other government agencies and private companies – President Joe Biden is considering how to respond. It’s not clear exactly what data the hackers actually stole in the time they had access, roughly from March through December 2020, but they exploited software made by the Texas-based firm SolarWinds to gain access to key research and security information, including research for future nuclear weapons.

International trade and cyber conflict: Decomposing the effect of trade on state-sponsored cyber attacks
A state’s decision to engage in cyber operations has important implications for its trade. Successful cyber espionage could yield valuable trade secrets that could boost domestic production and spur economic growth. On the other hand, uncovered cyber operations could invite devastating sanctions that retard economic development. In spite of this, the nexus between trade and cyber attacks has received little attention in the literature. In this article, I explore how a state’s trade relations affect its propensity to engage in cyber attacks.
